Personally, MongoBleed reveals a gap. Patching immediately is the only logical step.#MongoBleed #Cybersecurity
Quick Video Breakdown: This Blog Article
This video clearly explains this blog article.
Even if you don’t have time to read the text, you can quickly grasp the key points through this video. Please check it out!
If you find this video helpful, please follow the YouTube channel “AIMindUpdate,” which delivers daily AI news.
https://www.youtube.com/@AIMindUpdate
Read this article in your native language (10+ supported) 👉
[Read in your language]
Unpacking MongoDB’s MongoBleed Vulnerability: Enterprise Risks and Mitigation Strategies
👍 Recommended For: IT Managers overseeing database security, Cybersecurity Analysts monitoring enterprise threats, CTOs evaluating ROI impacts from data breaches
John: Alright, folks, let’s cut through the noise. In the world of enterprise databases, MongoDB has been a go-to for its flexibility and scalability—handling everything from e-commerce backends to real-time analytics. But here’s the harsh engineering reality: even battle-tested tech like MongoDB isn’t immune to flaws that can punch holes in your security posture. Enter CVE-2025-14847, dubbed “MongoBleed,” a high-severity vulnerability that’s already under active exploitation as of early 2026. This isn’t just a minor glitch; it’s a memory leakage issue that could expose sensitive data without authentication, potentially costing businesses millions in breaches, downtime, and compliance fines. If your organization relies on MongoDB for critical workflows, ignoring this is like leaving your factory doors wide open during a heist spree. We’re talking industry bottlenecks where unpatched systems lead to data leaks, regulatory headaches, and eroded customer trust—issues that directly hit your bottom line.
The “Before” State: Traditional Risks in Database Management
Before diving into MongoBleed, let’s contrast the old school of database security with the urgent need for proactive patching. Traditionally, enterprises have treated databases like MongoDB as set-it-and-forget-it infrastructure. You’d deploy a version, configure authentication, and assume firewalls or access controls would handle the rest. But pain points abound: outdated versions linger due to migration fears, compression features like zlib are enabled by default for efficiency, and monitoring for zero-day exploits? Often an afterthought until a breach hits.
Lila: Think of it like maintaining a classic car. You might love the ride, but without regular checks, that engine leak turns into a full breakdown on the highway. In MongoDB’s case, before awareness of MongoBleed, admins enabled zlib compression to speed up data transfers and reduce storage costs—great for ROI in high-volume environments. But this “before” state left systems vulnerable to unauthenticated attacks, where attackers could send crafted queries to leak uninitialized heap memory, potentially grabbing credentials, API keys, or customer data. The trade-off? What seemed like optimized workflows turned into ticking time bombs, with over 87,000 exposed instances worldwide as reported by security firms like Wiz and Tenable.
The real kicker: traditional methods relied on post-incident forensics, leading to reactive firefighting. Businesses faced skyrocketing costs from data recovery (averaging $4.45 million per breach, per recent IBM reports) and lost productivity during outages. No analogies here—just cold, hard business logic: unpatched flaws amplify risks in critical sectors like healthcare and finance, where downtime isn’t an option.
Core Mechanism: How MongoBleed Works and Why It Matters
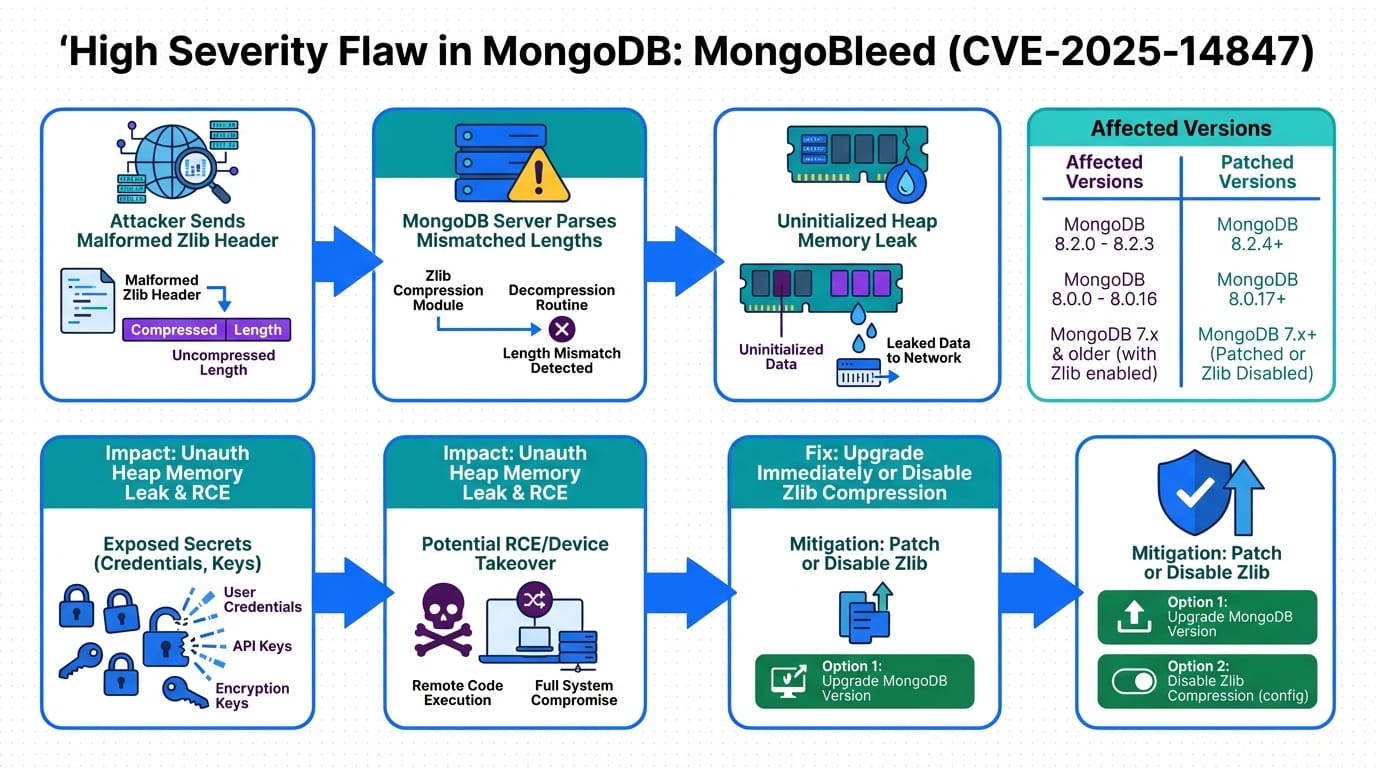
John: From an executive-summary perspective, MongoBleed stems from a flaw in how MongoDB handles zlib compression during data decompression. Structurally, when an unauthenticated user sends a specially crafted compressed message, the server decompresses it but fails to properly initialize the memory buffer. This leads to leakage of uninitialized heap memory—bits of data lingering from previous operations. It’s not a full remote code execution, but it’s bad enough: attackers can extract sensitive info like passwords or tokens without logging in.
To break it down with structured reasoning: MongoDB versions from 4.4 to 7.0 are affected, as detailed in advisories from MongoDB and security outlets like The Hacker News. The vulnerability scores a CVSS of 7.5 (high severity) because it’s remotely exploitable over the network with low complexity. Engineering trade-offs? Zlib was meant to boost performance and cut bandwidth costs, but this bug flips it into a liability. Mitigation is straightforward: upgrade to patched versions (e.g., 7.0.15 or 6.0.18) or disable zlib via configuration flags. But here’s the insight—[Important Insight] patching isn’t just about compliance; it’s a direct ROI play, preventing potential losses that dwarf upgrade efforts.
Lila: For those new to this, imagine your database as a filing cabinet. Zlib compression is like zipping files to save space, but MongoBleed is a faulty zipper that spills out random papers from other drawers when you unzip. No deep dives into code here, but know that tools like proof-of-concept exploits (e.g., the “mongobleed” PoC released on GitHub) make this easy for attackers, as noted in Cybersecurity News.
Use Cases: Real-World Scenarios Where MongoBleed Hits Hard
Let’s ground this in practical value with three concrete enterprise scenarios.
First, consider a fintech company using MongoDB for transaction logging. An attacker exploits MongoBleed to leak API keys, enabling fraudulent transactions. Pre-patch, this could lead to financial losses exceeding $1 million and regulatory scrutiny under GDPR or PCI-DSS. Post-mitigation? Secure operations resume with minimal disruption.
Second, in healthcare, where MongoDB stores patient records, a leak could expose PHI (Protected Health Information). Imagine a hospital’s system hit during peak hours—downtime delays treatments, and breaches trigger HIPAA fines. Upgrading ensures data integrity, preserving trust and operational flow.
Third, for e-commerce platforms scaling with MongoDB’s NoSQL flexibility, MongoBleed could reveal customer credentials, fueling identity theft. Businesses like these see ROI boosts from quick patches, turning potential PR nightmares into demonstrations of robust security postures.
Comparison Table: Old Method vs. New Solution
| Aspect | Old Method (Unpatched MongoDB) | New Solution (Patched/Configured MongoDB) |
|---|---|---|
| Security Risk | High—Unauthenticated memory leaks expose sensitive data | Low—Patches fix zlib handling, preventing leaks |
| Performance Trade-offs | Compression enables speed but introduces vulnerabilities | Disable zlib or upgrade for secure, optimized ops |
| Cost Implications | High breach costs, downtime losses | Lower ROI hits via preventive measures |
| Implementation Effort | Reactive patching after exploitation | Proactive upgrades using official MongoDB guides |
Conclusion: Key Insights and Next Steps
John: Wrapping this up, MongoBleed underscores a timeless engineering truth: tech evolves, but so do threats. By understanding the flaw’s mechanics and acting swiftly—whether upgrading to secure versions or disabling vulnerable features—you safeguard your enterprise’s data and maximize ROI. Shift your mindset from reactive to proactive: integrate vulnerability scanning tools like Tenable or Wiz into your workflows, and monitor CISA’s Known Exploited Vulnerabilities catalog for real-time alerts.
Lila: Next steps? Audit your MongoDB deployments today, test patches in staging environments, and train teams on secure configurations. Remember, security isn’t a cost—it’s an investment in resilience.
John: Senior Tech Lead at AI Mind Update, with 15+ years in software engineering and a passion for demystifying complex systems.
Lila: Pragmatic developer bridging tech gaps for beginners, ensuring accessible insights in every post.
References & Further Reading
- High severity flaw in MongoDB could allow memory leakage | CSO Online
- MongoDB Vulnerability CVE-2025-14847 Under Active Exploitation Worldwide – The Hacker News
- MongoBleed: Critical MongoDB Vulnerability CVE-2025-14847 | Wiz Blog
- MongoBleed defect swirls, stamping out hope of year-end respite | CyberScoop
- MongoBleed CVE-2025-14847 exploited in the wild | Tenable
